Threat Intelligence
Strategic Threat Intelligence: Transforming Data into Actionable Defense
Threat intelligence is the lifeblood of modern cybersecurity—transforming raw data into contextual, actionable insights that empower organizations to anticipate, prevent, and respond to cyber threats with precision and speed. At Cyborgenic, we deliver intelligence-driven security that moves your organization from reactive defense to proactive protection.


What Makes True Threat Intelligence?
Threat intelligence goes beyond simple threat data by providing
Organization-Specific Insights
- Customized analysis of your unique attack surface
- Asset-specific vulnerability mapping
- Industry-targeted threat actor profiling
- Business-context risk prioritization
Detailed Contextual Understanding
- Comprehensive threat actor TTPs (Tactics, Techniques, Procedures)
- Campaign analysis and attribution
- Indicator of Compromise (IoC) correlation
- Attack vector evolution tracking
Actionable Defense Guidance
- Prioritized remediation recommendations
- Proactive control implementation
- Detection rule optimization
- Incident response enhancement
The Cyborgenic Threat Intelligence Lifecycle
- Strategic Planning & Requirements Definition
We collaborate with your stakeholders to define intelligence objectives aligned with business goals.
Key Activities:
- Executive leadership threat briefings
- Department-specific risk assessment
- Compliance requirement mapping
- Intelligence gap analysis
- Multi-Source Intelligence Collection
We aggregate threat data from diverse, validated sources to build comprehensive threat awareness.
Collection Channels:
- Commercial Feeds: Curated intelligence from leading providers
- Open-Source Intelligence (OSINT): Public threat monitoring
- Dark Web Monitoring: Underground forum and marketplace surveillance
- Industry ISACs: Sector-specific threat sharing
- Proprietary Sensors: Custom deployment for unique threat landscapes


- Advanced Processing & Correlation
Our analytics engine transforms raw data into structured intelligence.
Processing Capabilities:
- AI-powered pattern recognition
- MITRE ATT&CK framework mapping
- False positive filtering and validation
- Cross-source correlation and enrichment
- Expert-Led Analysis & Insight Generation
Our security analysts provide human expertise that machines cannot replicate.
Analytical Outputs:
- Campaign analysis and threat actor profiling
- Vulnerability exploitation likelihood assessment
- Attack path modeling and simulation
- Business impact analysis
- Integrated Dissemination & Action
We deliver intelligence where and when it’s needed most.
Delivery Channels:
- Real-time API integration with security tools
- Automated alerting and notification systems
- Customized reporting for different stakeholders
- Direct integration with SIEM, SOAR, and EDR platforms
- Continuous Feedback & Optimization
We ensure intelligence remains relevant and effective through ongoing refinement.
Optimization Processes:
- Stakeholder feedback incorporation
- Intelligence requirement validation
- Control effectiveness measurement
- Program maturity assessment
Our Threat Intelligence Service Tiers
Strategic Intelligence
For Executive Leadership & Board
- Global threat landscape analysis
- Industry risk benchmarking
- Regulatory impact assessment
- Investment guidance and ROI analysis
Deliverables:
- Quarterly executive briefings
- Risk management dashboards
- Strategic planning support
- Compliance alignment reporting

Operational Intelligence
For Security Operations & Incident Response
- Threat actor TTP analysis
- Campaign tracking and attribution
- Detection rule development
- Response playbook enhancement
Deliverables:
- Weekly threat updates
- TTP deep-dive reports
- Hunting hypothesis generation
- Control gap analysis
Tactical Intelligence
For Technical Teams & Automation
- Real-time IoC dissemination
- Malware analysis and reverse engineering
- Vulnerability prioritization
- Automated response triggering
Deliverables:
- Daily IOC feeds
- Malware analysis reports
- Integration-ready data formats
- Automated block lists


Measurable Business Impact
Enhanced Security Effectiveness
- 70% faster threat detection through intelligence-led monitoring
- 60% reduction in false positives via contextual alerting
- 45% improvement in prevention capabilities through proactive controls
- 80% faster incident investigation with enriched context
Operational Efficiency
- 50% reduction in manual threat research time
- 65% faster security control tuning and optimization
- 40% improvement in resource allocation efficiency
- 75% faster compliance reporting and evidence collection
Risk Reduction & Cost Savings
- 55% decrease in successful cyber attacks
- 30% reduction in security incident costs
- 85% improvement in risk-based decision making
- Potential USD 1M+ savings in breach detection and escalation costs
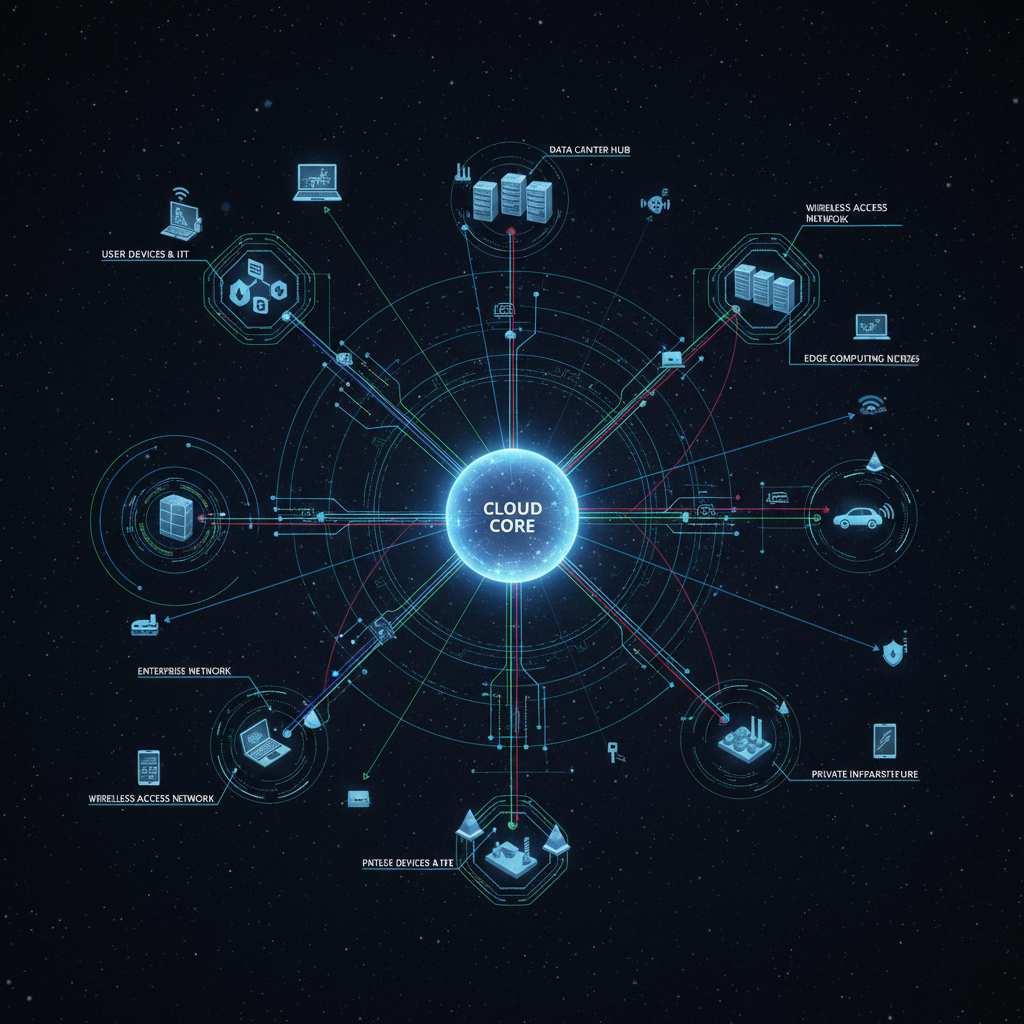
Integration with Your Security Ecosystem
Security Operations Center (SOC) Enhancement
- Intelligence-led alert triage and prioritization
- Context enrichment for incident investigation
- Hunting campaign development based on TTPs
- Performance metrics and reporting
Vulnerability Management
- Exploitation likelihood-based prioritization
- Patch management optimization
- Compensating control recommendation
- Risk-based vulnerability scoring
Incident Response
- Rapid threat context during investigations
- Adversary behavior prediction and tracking
- Response action effectiveness assessment
- Post-incident intelligence gathering


Why Choose Cyborgenic Threat Intelligence?
Expert-Led Analysis
Our intelligence team brings:
- Former government and military intelligence experience
- Industry-specific threat expertise
- Advanced analytical certifications and training
- Real-world incident response background
Proven Methodology
- Mature intelligence lifecycle management
- Quality-controlled analysis processes
- Actionable reporting standards
- Continuous improvement framework
Technology Integration
- Pre-built connectors for major security platforms
- API-based integration capabilities
- Custom integration development
- Performance optimization support
In the cybersecurity arms race, intelligence is your strategic advantage.
Transform your security operations from reactive to predictive with Cyborgenic’s Threat Intelligence services.
