Network Architecture Review
Network Architecture Security Review: Building a Resilient Network Foundation
Your network architecture forms the backbone of your digital operations. In an era of sophisticated cyber threats, a secure, well-designed network is not just an IT requirement—it’s a business imperative. At Cyborgenic, our Network Architecture Security Review provides a comprehensive assessment of your network design, identifying security gaps and providing a strategic roadmap to build a resilient, future-proof infrastructure.


The Critical Need for Network Architecture Review
Concerning Statistics:
- 68% of organizations have experienced network security incidents due to architectural flaws
- 52% of data breaches involve weaknesses in network segmentation
- 74% of companies lack proper network access controls
- 89% of organizations have outdated network security policies
Our Comprehensive Review Methodology
Phase 1: In-Depth Discovery & Information Gathering
We begin by building a complete understanding of your network ecosystem through multiple approaches
Documentation Analysis:
- Network architecture diagrams and topology maps
- Security requirements and compliance frameworks
- Technology inventory and asset management records
- DMZ configurations and perimeter security designs
- Existing security policies and procedures
Stakeholder Engagement:
- Interviews with network architects and engineers
- Discussions with security analysts and IT management
- Leadership alignment on business objectives
- Cross-functional team workshops


Phase 2: Technical Architecture Assessment
Our security engineers conduct a thorough examination of your network design:
Network Segmentation & Zoning:
- Security zone boundaries and trust relationships
- Micro-segmentation implementation effectiveness
- VLAN configuration and isolation verification
- East-west traffic control assessment
Access Control Framework:
- Network Access Control (NAC) implementation
- Role-Based Access Control (RBAC) policies
- Third-party and partner access management
- Privileged access pathways and controls
Security Control Evaluation:
- Firewall rule base analysis and optimization
- Intrusion Prevention/Detection System (IPS/IDS) configuration
- Network monitoring and logging capabilities
- Security technology integration effectiveness
Phase 3: Risk Analysis & Strategic Recommendations
We translate technical findings into actionable business insights:
Gap Analysis:
- Missing security controls and compensating mechanisms
- Incomplete or improperly implemented security measures
- Compliance requirement alignment verification
- Industry best practice comparison
Threat Modeling:
- Attack surface analysis and vulnerability mapping
- Potential attack path identification
- Business impact assessment of identified risks
- Risk prioritization based on likelihood and impact

Key Assessment Areas
Network Security Architecture
- Defense-in-depth strategy evaluation
- Perimeter security effectiveness
- Internal network protection mechanisms
- Cloud and hybrid environment security
Access Management
- User authentication and authorization processes
- Device onboarding and compliance verification
- Guest network security controls
- Remote access and VPN security
Third-Party Integration
- Partner connectivity security assessment
- Supply chain network access review
- External service integration security
- Data exchange protocol evaluation
Business Continuity
- Network redundancy and failover capabilities
- Disaster recovery network architecture
- Incident response network preparedness
- High-availability design validation
Our Deliverables: Actionable Security Intelligence
Executive Summary Report
- Business-focused risk analysis and recommendations
- Strategic security posture assessment
- High-level findings and immediate action items
- Compliance status and regulatory alignment
Detailed Technical Assessment
- Comprehensive vulnerability analysis with evidence
- Network topology maps with security annotations
- Configuration review findings and remediation steps
- Security control effectiveness ratings

Risk-Prioritized Findings
Critical Risks (Immediate Action Required):
- Architectural flaws enabling direct compromise
- Missing fundamental security controls
- Compliance violations with immediate impact
High Risks (30-60 Day Remediation):
- Significant security control gaps
- Inadequate segmentation and access controls
- Monitoring and detection weaknesses
Medium Risks (Strategic Improvements):
- Optimization opportunities
- Process and policy enhancements
- Advanced security capabilities
Remediation Roadmap
Immediate Actions (0-30 Days):
- Critical vulnerability mitigation
- Emergency configuration changes
- Compensating control implementation
Short-term Initiatives (30-90 Days):
- Security control enhancements
- Policy and procedure updates
- Staff training and awareness
Strategic Projects (90-180 Days):
- Architectural improvements
- Technology modernization
- Advanced security implementation

The Cyborgenic Advantage
Expert-Led Assessment
Our team brings deep expertise in:
- Enterprise network architecture design
- Zero Trust architecture implementation
- Cloud and hybrid network security
- Industry compliance requirements (NIST, CIS, ISO 27001)
Business-Aligned Approach
We ensure our recommendations:
- Support business objectives and operational requirements
- Consider cost-effectiveness and ROI
- Align with organizational risk appetite
- Enable future growth and scalability
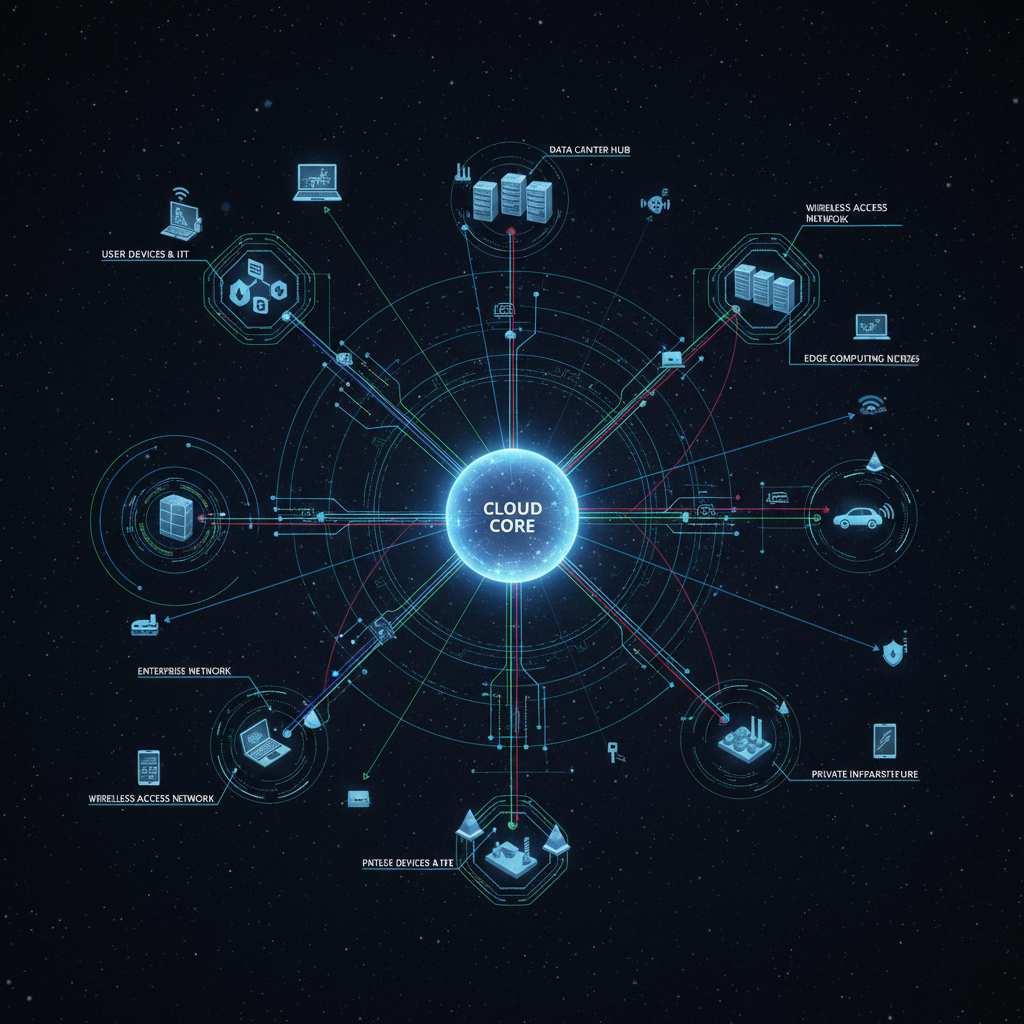
Comprehensive Coverage
We assess your entire network ecosystem:
- On-premises infrastructure and data centers
- Cloud and hybrid cloud environments
- Remote workforce connectivity
- IoT and operational technology networks
Why Choose Cyborgenic for Your Network Architecture Review?
Proactive Risk Management
Identify and address architectural weaknesses before they lead to:
- Data breaches and system compromises
- Regulatory compliance violations
- Service disruptions and downtime
- Reputational damage and financial loss
Strategic Security Planning
Transform your network from a vulnerability to a strength:
- Future-proof your architecture against emerging threats
- Optimize security investments and resource allocation
- Establish a foundation for Zero Trust implementation
- Enable digital transformation with confidence
Compliance Assurance
Ensure your network architecture meets:
- Industry regulations (PCI-DSS, HIPAA, GDPR)
- Security frameworks (NIST CSF, CIS Controls)
- Internal security policies and standards
- Customer and partner security requirements


Our Engagement Model
Standard Assessment Timeline
- Week 1-2: Discovery and information gathering
- Week 3-4: Technical assessment and analysis
- Week 5: Reporting and recommendations
- Week 6: Presentation and roadmap development
Flexible Service Packages
Essential Review:
- Basic network architecture assessment
- High-level recommendations
- Compliance gap analysis
Comprehensive Assessment:
- Detailed technical analysis
- Strategic remediation roadmap
- Ongoing consultation support
Enterprise Architecture Program:
- Continuous architecture review
- Security design partnership
- Transformation program support
Your network architecture shouldn’t be your biggest security risk.
Let Cyborgenic’s network security experts assess your infrastructure and build a resilient foundation for business growth.
