Data Protection
Strategic Data Protection: Transforming Compliance into Competitive Advantage
In the digital economy, data is your most valuable asset—and your greatest liability. Between sophisticated cyber threats, stringent regulations like the GDPR and DPDPA, and rising consumer privacy expectations, data protection can no longer be an IT afterthought. It is a strategic imperative integral to brand trust, operational integrity, and market credibility. Our Data Protection service provides a complete framework, moving you from a state of reactive compliance to proactive data stewardship. We empower you to not only safeguard sensitive information but to leverage strong privacy practices as a cornerstone of customer confidence and business resilience.

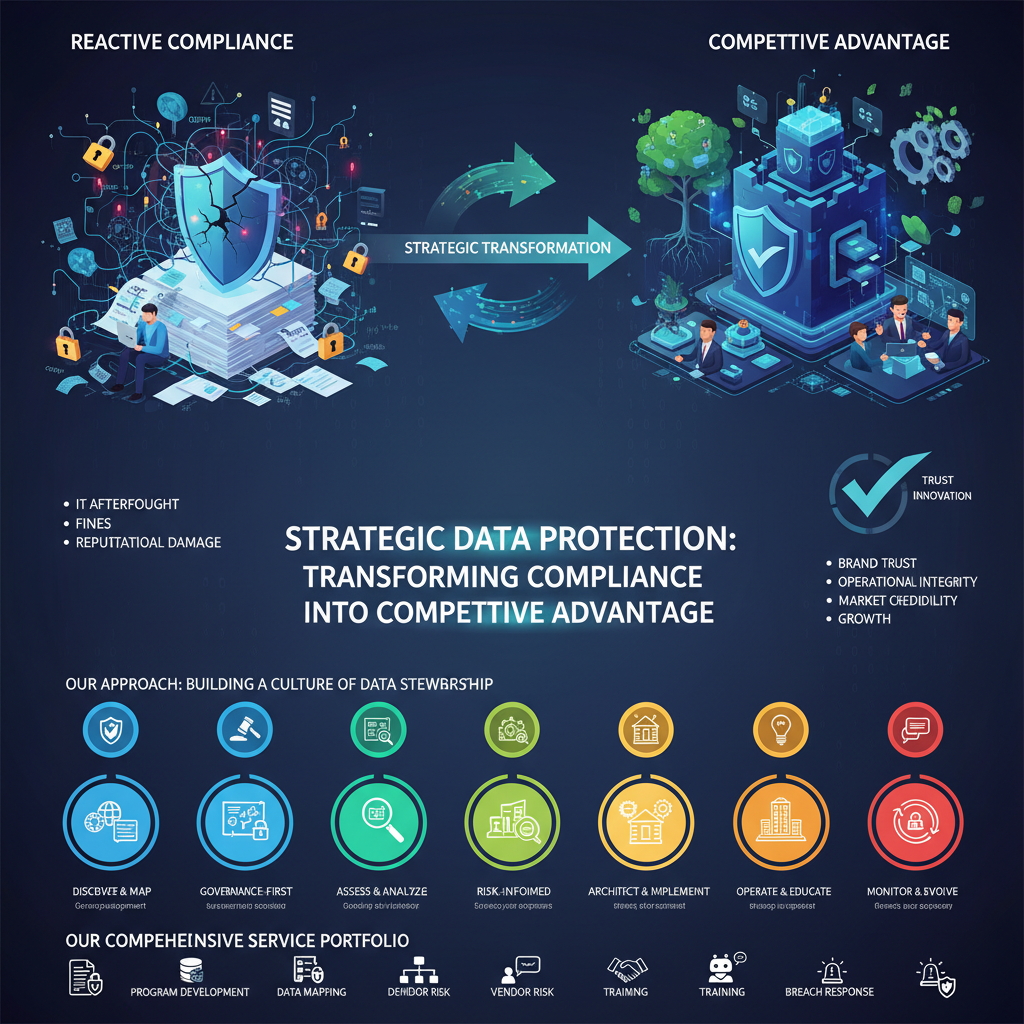
Our Approach: Building a Culture of Data Stewardship
We believe effective data protection is a continuous journey, not a one-time project. Our approach is built on three core pillars:
- Governance-First Foundation: We begin by establishing clear accountability, policies, and processes. Protection starts with leadership and a defined framework.
- Privacy by Design & Default: We integrate data protection principles into the very fabric of your projects, products, and processes from the outset, reducing risk and cost downstream.
- Risk-Informed Prioritization: Our actions are guided by a clear understanding of what data you have, where it flows, and the real-world business impact of its compromise or misuse.
Our Methodology: A Phased Path to Maturity
We employ a structured, multi-phase methodology to systematically build and enhance your data protection capabilities.
Phase 1: Discover & Map
You cannot protect what you do not know. We begin by creating visibility.
- Data Inventory & Classification: Identify and catalog all personal and sensitive data across your organization, classifying it based on sensitivity and regulatory requirements.
- Data Flow Mapping: Visualize how data moves through your organization, across departments, and to third-party vendors, pinpointing points of risk and unnecessary retention.


Phase 2: Assess & Analyze
With a map in hand, we assess your current posture against standards and threats.
- Gap Assessment: Evaluate your policies, controls, and procedures against relevant regulations (GDPR, DPDPA, CCPA) and frameworks (ISO 27701).
- Risk Assessment: Conduct a dedicated Data Protection Impact Assessment (DPIA) for high-risk processing activities to identify and quantify privacy risks.
Phase 3: Architect & Implement
We translate analysis into action, building and strengthening your controls.
- Policy & Procedure Development: Craft clear, actionable data privacy policies, incident response plans, and data subject request procedures.
- Control Implementation: Guide the deployment of technical and organizational measures—from access controls and encryption to data retention schedules and vendor management protocols.
Phase 4: Operate & Educate
Protection is sustained through daily practice and awareness.
- Training & Awareness Programs: Develop role-specific training to foster a company-wide culture of data responsibility, from the boardroom to the front lines.
- Process Integration: Embed privacy checkpoints into HR, marketing, and development lifecycles (Privacy by Design).
Phase 5: Monitor & Evolve
We ensure your program adapts to change.
- Ongoing Compliance Monitoring: Track regulatory changes and audit control effectiveness.
- Incident Response Support: Provide expert guidance to prepare for and manage potential data breaches.
- Program Maturity Reviews: Periodically reassess and advance your program to address new business initiatives and threats.


Our End-to-End Process
For every engagement, we follow a clear, collaborative process:
- Stakeholder Kickoff: Align with legal, IT, security, and business unit leaders on scope, goals, and success metrics.
- Workshops & Interviews: Engage with process owners to map data flows and understand current practices.
- Technical & Documentation Review: Analyze system configurations, contracts, and existing policies.
- Analysis & Reporting: Develop findings, risk ratings, and a prioritized remediation roadmap.
- Roadmap Execution Support: Assist your team in implementing recommendations, from policy rollout to tool configuration.
- Knowledge Transfer & Review: Ensure ongoing ownership with formal handoff and scheduled maturity assessments.
Our Comprehensive Service Portfolio
- Data Protection Program Development: Build a standalone privacy framework or integrate with your ISMS.
- Data Mapping & Inventory Services: Gain full visibility into your data landscape.
- DPIA (Data Protection Impact Assessment) Facilitation: Proactively manage high-risk processing.
- Vendor Risk Management: Assess and contractually bind third parties to protect shared data.
- Data Subject Request (DSR) Automation: Streamline processes for access, deletion, and portability requests.
- Privacy Awareness Training: Tailored programs for employees, developers, and executives.
- Breach Response Planning & Support: Develop and test your incident response playbook.


The Business Value of Robust Data Protection
- Enhanced Trust & Reputation: Demonstrate your commitment to privacy, strengthening customer and partner relationships.
- Reduced Financial Risk: Avoid devastating regulatory fines, litigation costs, and remediation expenses.
- Operational Efficiency: Streamline data management, reduce redundant storage, and clarify data handling processes.
- Competitive Differentiation: Use strong data governance as a market differentiator in tender processes.
- Informed Innovation: Enable safe and compliant use of data for analytics and new business models.
Secure Your Data, Sustain Your Growth
Protecting data is more than a legal requirement—it’s a critical business function. Partner with us to build a data protection program that fuels trust, mitigates risk, and supports your strategic ambitions.
Ready to make data protection a pillar of your strength?
Contact our experts to begin your assessment.
Email: sales@cyborgenic.com | Phone: +91 97732 98161
Transform your data liability into a legacy of trust

