Configuration Review
Configuration Review: The Foundation of Cybersecurity Resilience
In an era where cyber threats evolve daily, proactive security measures are no longer optional—they’re essential for business survival. At Cyborgenic, we believe that proper configuration forms the bedrock of any robust cybersecurity program. A configuration review is not just a compliance requirement; it’s a strategic imperative that identifies and rectifies security gaps before attackers can exploit them.


Understanding Configuration Reviews
A configuration review is a systematic examination of your IT systems, applications, and security controls to ensure they’re configured according to security best practices and business requirements. These reviews identify misconfigurations, vulnerabilities, and weaknesses that could expose your organization to cyber threats.
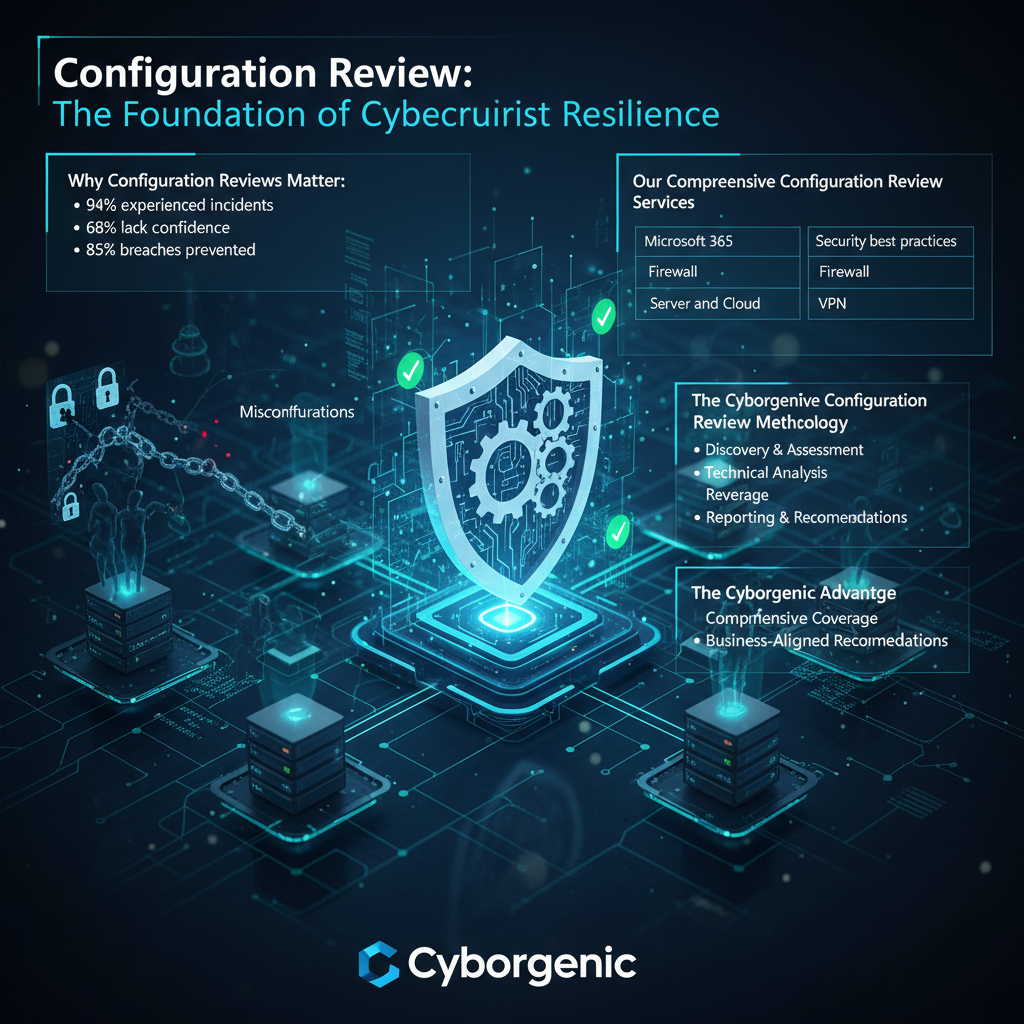
Why Configuration Reviews Matter:
- 94% of enterprises have experienced security incidents due to misconfigurations
- 68% of organizations lack confidence in their security configurations
- 43% of cloud data breaches result from misconfigured resources
- Regular reviews can prevent 85% of common security breaches
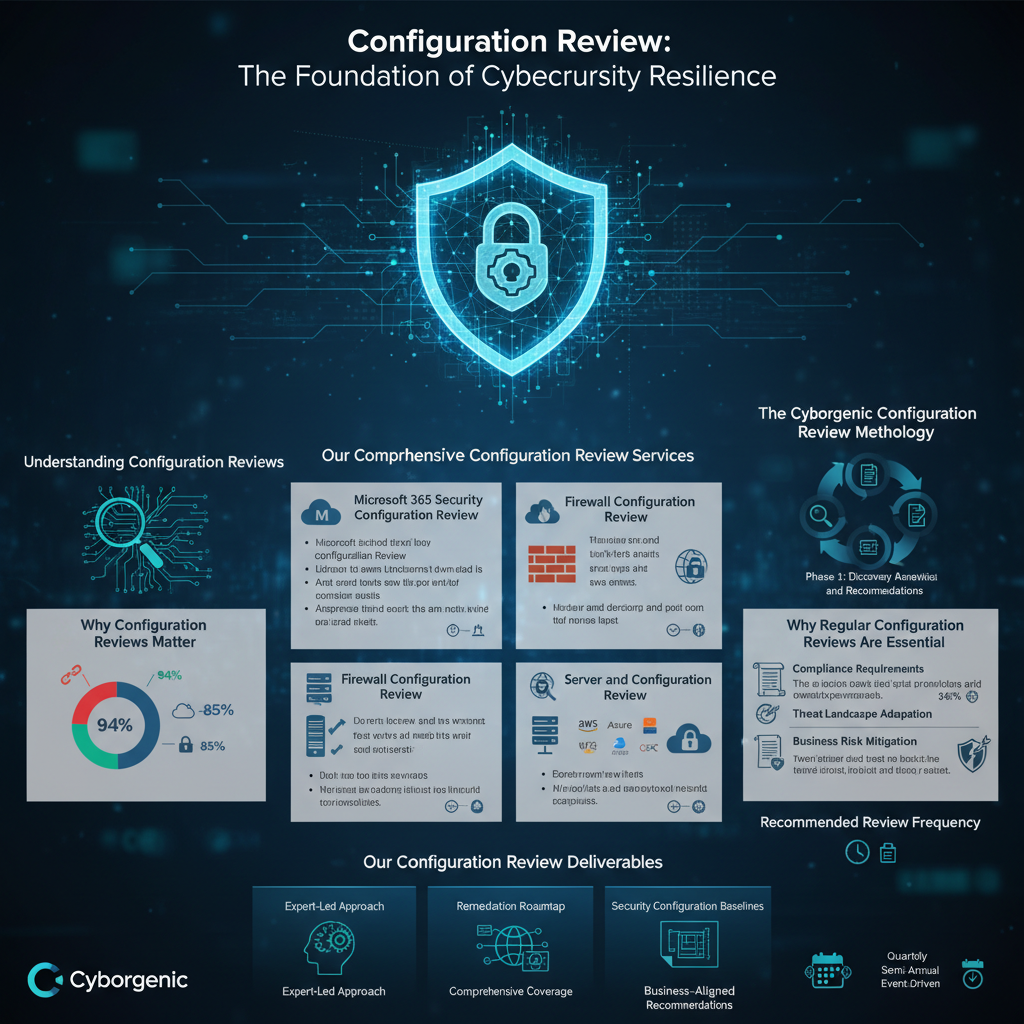
Our Comprehensive Configuration Review Services
Microsoft 365 Security Configuration Review
As organizations increasingly rely on Microsoft 365, ensuring its security configuration is paramount.
Our Assessment Covers:
- Identity and Access Management (Azure AD configuration)
- Data Loss Prevention (DLP) policies and effectiveness
- Threat protection settings and alert configurations
- Compliance center configurations and reporting
- SharePoint and OneDrive security settings
- Exchange Online protection mechanisms
Key Focus Areas:
- Multi-factor authentication implementation
- Conditional access policies
- Data encryption and rights management
- User permission audits and review processes
Firewall Configuration Review
Firewalls serve as your network’s primary defense perimeter. Proper configuration is critical for effective protection.
Our Assessment Includes:
- Rule base analysis and optimization
- Access control list (ACL) review
- Network address translation (NAT) policies
- VPN configuration security
- Intrusion prevention system (IPS) settings
- Logging and monitoring configurations
Critical Security Checks:
- Default rule analysis and cleanup
- Unnecessary service exposure
- Proper segmentation between security zones
- Regular rule base maintenance procedures


VPN Configuration Review
With remote work becoming standard, VPN security is more crucial than ever.
Our Evaluation Covers:
- Authentication mechanisms and strength
- Encryption protocols and key management
- Access control and user permissions
- Logging and monitoring capabilities
- Split tunneling configurations
- Client security requirements
Server and Cloud Configuration Review
Servers and cloud environments house your most critical assets and data.
OurComprehensiveAssessment:
On-Premises Servers:
- Operating system hardening
- Service configuration and minimization
- Patch management processes
- Access control and privilege management
Cloud Infrastructure (AWS, Azure, GCP):
- Identity and Access Management (IAM) policies
- Storage configuration and encryption
- Network security groups and rules
- Logging and monitoring setup
- Compliance with cloud security benchmarks
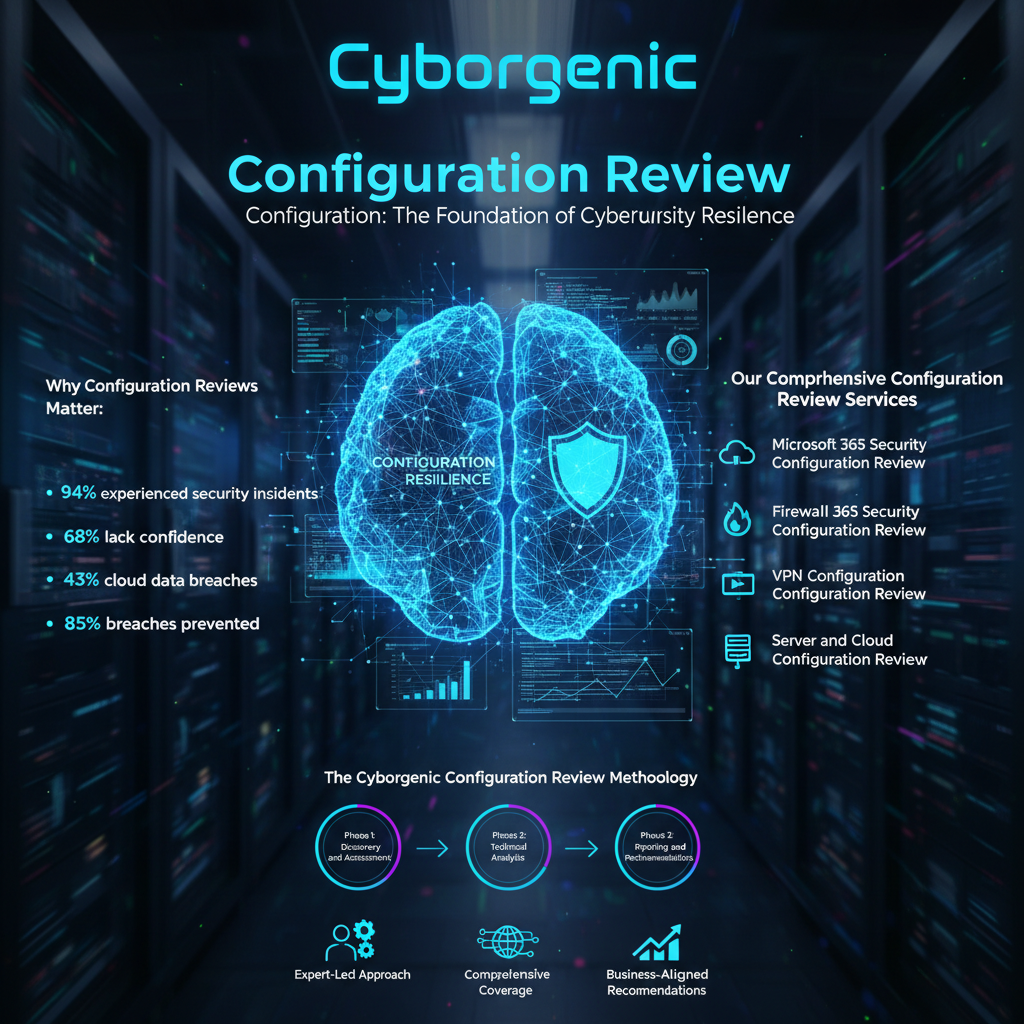

The Cyborgenic Configuration Review Methodology
Phase 1: Discovery and Assessment
- Comprehensive inventory of systems and applications
- Current configuration documentation review
- Stakeholder interviews to understand business requirements
- Compliance framework alignment (NIST, CIS, ISO 27001)
Phase 2: Technical Analysis
- Automated scanning using industry-leading tools
- Manual validation of critical configurations
- Security control effectiveness testing
- Vulnerability assessment and risk scoring
Phase 3: Reporting and Recommendations
- Detailed findings with risk prioritization
- Specific remediation guidance
- Configuration templates and benchmarks
- Ongoing maintenance recommendations
Why Regular Configuration Reviews Are Essential
Compliance Requirements
Many regulatory frameworks mandate regular configuration reviews:
- PCI DSS: Requires quarterly reviews of security controls
- HIPAA: Mandates security configuration management
- SOC 2: Includes configuration management as key controls
- GDPR: Requires appropriate security configurations
Threat Landscape Adaptation
- New vulnerabilities discovered daily require configuration adjustments
- Emerging attack techniques target common misconfigurations
- Business changes often introduce new security gaps
- Technology updates can reset or change security settings
Business Risk Mitigation
Proper configuration reviews help prevent:
- Data breaches and unauthorized access
- Service disruptions and downtime
- Compliance violations and fines
- Reputational damage and customer loss

Our Configuration Review Deliverables
Comprehensive Assessment Report
- Executive summary for leadership
- Detailed technical findings
- Risk-based prioritization matrix
- Evidence documentation and screenshots
Remediation Roadmap
- Immediate actions (0-30 days) for critical risks
- Short-term improvements (30-90 days)
- Long-term strategic recommendations
- Step-by-step implementation guidance
Security Configuration Baselines
- Customized configuration templates
- Automated compliance checking scripts
- Ongoing monitoring recommendations
- Policy and procedure documentation
The Cyborgenic Advantage
Expert-Led Approach
Our security consultants bring:
- Industry certifications (CISSP, CISM, CCSP)
- Vendor-specific expertise (Microsoft, Cisco, AWS, Azure)
- Real-world experience securing complex environments
- Deep understanding of regulatory requirements
Comprehensive Coverage
We review your entire technology stack:
- Network infrastructure and security devices
- Cloud platforms and SaaS applications
- Servers and endpoints
- Identity and access management systems
Business-Aligned Recommendations
We prioritize findings based on:
- Actual business impact and risk exposure
- Operational efficiency considerations
- Cost-effectiveness of remediation
- Long-term security posture improvement


Recommended Review Frequency
Quarterly Reviews:
- High-change environments
- Regulated industries
- Organizations with significant remote workforce
- Businesses handling sensitive data
Semi-Annual Reviews:
- Stable environments with minimal changes
- Organizations with mature security programs
- Non-regulated industries with standard risk profiles
Event-Driven Reviews:
- Following major system changes or upgrades
- After security incidents or breaches
- During technology platform migrations
- When new compliance requirements emerge
Don’t let misconfigurations become your weakest link.
Partner with Cyborgenic for comprehensive configuration reviews that transform your security posture from vulnerable to vigilant.
