ASV Scan
Understanding ASV Vulnerability Scans: Your Guide to PCI DSS Compliance
For any organization handling payment card data, PCI DSS compliance isn’t optional—it’s mandatory. Among the critical requirements is regular vulnerability scanning, specifically mandating the use of Approved Scanning Vendors (ASV) for external assessments. At Cyborgenic, we simplify this complex requirement, ensuring your organization meets and maintains compliance while strengthening your security posture.


The PCI DSS ASV Scanning Requirement
PCI DSS Requirement 11.2.2 clearly states:
- Quarterly external vulnerability scans must be performed
- Scans must be conducted by a PCI SSC-approved ASV
- Rescans must occur until all high-risk vulnerabilities are remediated
- Documentation from the four most recent quarters must be maintained
Why ASV Scanning is Non-Negotiable
Regulatory Mandate
The Payment Card Industry Security Standards Council (PCI SSC) maintains strict standards for vulnerability scanning. Only ASVs with approved scanning solutions and methodologies can provide valid compliance reports that acquiring banks and payment processors will accept.
Expertise and Consistency
ASVs bring specialized expertise in:
- PCI DSS vulnerability classification and scoring
- Accurate identification of false positives
- Consistent scanning methodologies across assessment periods
- Up-to-date knowledge of emerging threats and vulnerabilities
Cost-Effective Compliance
While establishing an internal scanning capability might seem appealing, the costs of:
- Maintaining PCI SSC approval
- Keeping scan engines updated with the latest threat intelligence
- Ensuring consistent, accurate results meeting PCI standards
Far outweigh the investment in professional ASV services.

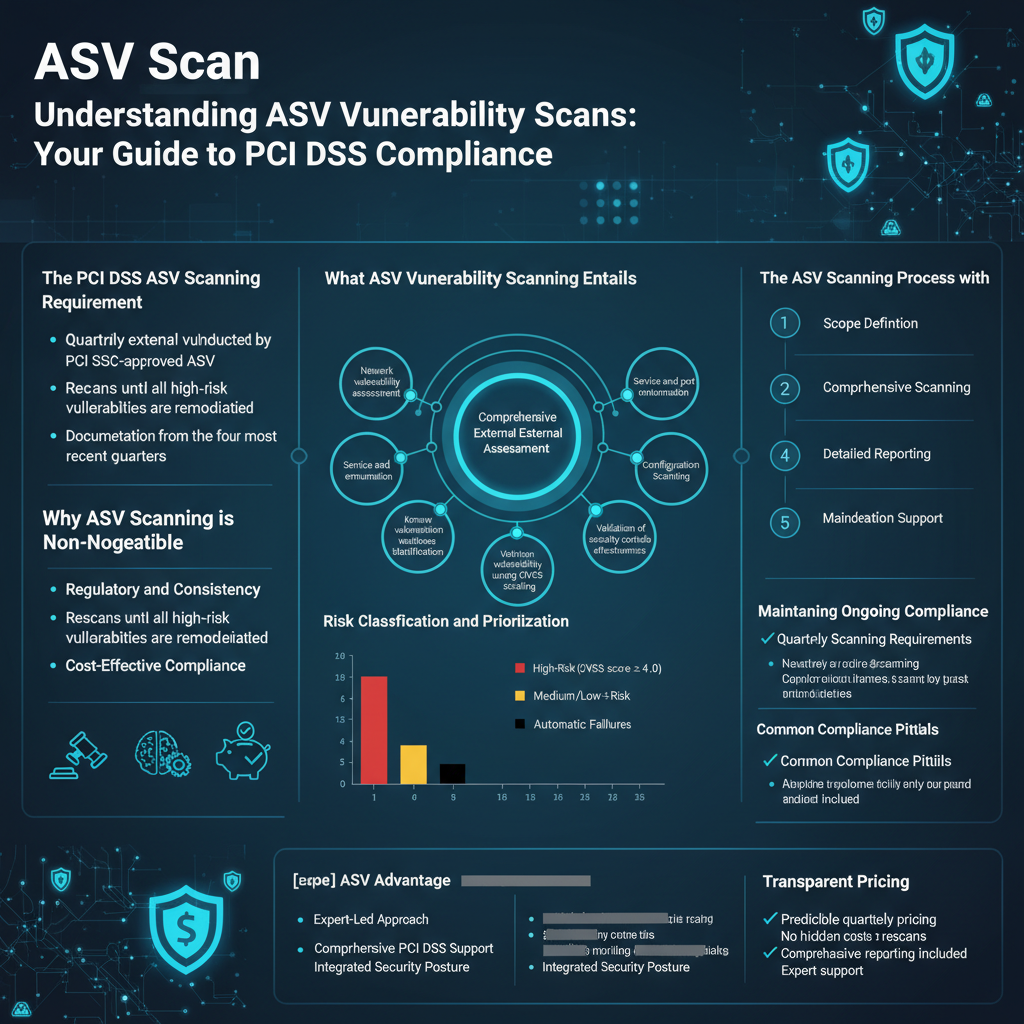
What ASV Vulnerability Scanning Entails
Comprehensive External Assessment
ASV scans examine your externally-facing systems from an attacker’s perspective, identifying vulnerabilities that could lead to cardholder data compromise.
Key Scanning Components:
- Network vulnerability assessment
- Service and port enumeration
- Configuration weakness identification
- Known vulnerability detection using CVSS scoring
- Validation of security controls effectiveness
Risk Classification and Prioritization
Vulnerabilities are classified according to PCI DSS requirements:
- High-Risk Vulnerabilities (CVSS score ≥ 4.0): Automatic scan failure
- Medium/Low-Risk Vulnerabilities: Documented for remediation
- Automatic Failures: Specific critical issues that immediately fail scans
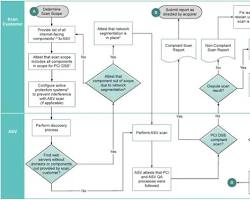
The ASV Scanning Process with Cyborgenic
- Scope Definition
We work with you to identify all in-scope systems, including:
- Web applications processing payments
- Network infrastructure components
- External-facing servers and services
- Third-party connections handling cardholder data
- Comprehensive Scanning
Our PCI SSC-approved scanning methodology includes:
- Non-intrusive vulnerability detection
- Authenticated scanning where appropriate
- Continuous monitoring during scan execution
- Immediate notification of critical findings


- Detailed Reporting
We provide comprehensive reports including:
- Executive summary for management review
- Technical findings with remediation guidance
- Compliance documentation for acquiring banks
- Risk-prioritized vulnerability listings
- Remediation Support
Our service extends beyond scanning to include:
- Vulnerability validation and false positive identification
- Remediation guidance and best practices
- Rescan coordination until compliance is achieved
- Ongoing consultation for maintaining scan compliance
Maintaining Ongoing Compliance
Quarterly Scanning Requirements
PCI DSS mandates scans must occur:
- At least quarterly throughout the year
- Following any significant network changes
- Within 90 days of the previous successful scan
- With documentation maintained for 12 months
Common Compliance Pitfalls
Organizations often struggle with:
- Scope Creep: Unidentified systems falling into CDE scope
- Remediation Delays: Extended time to address critical vulnerabilities
- Documentation Gaps: Incomplete records for audit purposes
- Configuration Drift: Systems falling out of compliance between scans

The Cyborgenic ASV Advantage
Expert-Led Approach
Unlike fully automated solutions, our ASV scanning includes:
- Security engineer review of all findings
- Context-aware vulnerability assessment
- Business-impact analysis of identified risks
- Personalized consultation throughout the process
Comprehensive PCI DSS Support
We provide end-to-end PCI compliance services:
- ASV vulnerability scanning and reporting
- Gap assessment against all PCI DSS requirements
- Remediation planning and implementation support
- Quarterly compliance validation and maintenance
Integrated Security Posture
Our ASV scanning integrates with broader security services:
- Continuous vulnerability management
- Penetration testing and security assessment
- Security awareness training
- Incident response planning
Getting Started with ASV Scanning
Simple Onboarding Process
- Scope Identification: Collaborative session to define scanning boundaries
- Scan Configuration: Tailored scanning profiles for your environment
- Initial Assessment: Comprehensive vulnerability discovery
- Remediation Planning: Prioritized action plan for compliance
- Continuous Compliance: Ongoing scanning and support
Transparent Pricing
Our ASV scanning services offer:
- Predictable quarterly pricing
- No hidden costs for rescans
- Comprehensive reporting included
- Expert support throughout the process

PCI compliance doesn’t have to be complicated. Let Cyborgenic handle your ASV scanning requirements while you focus on your business.
