AICPA SOC
Demystifying SOC Compliance
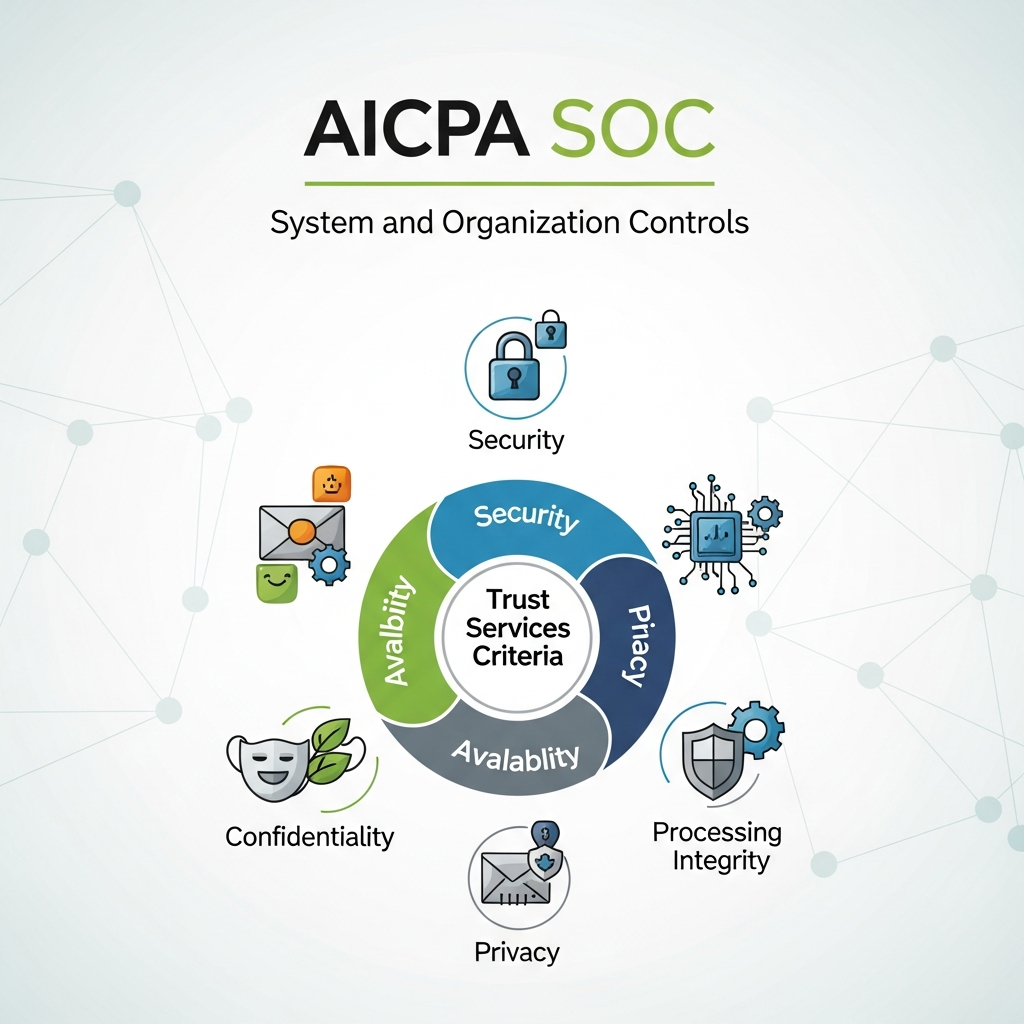
In today’s digital ecosystem, your clients need more than your word—they need verifiable proof that their data is safe in your hands. This is where SOC (System and Organization Controls) compliance comes in. It’s the gold standard for demonstrating your
organization’s commitment to security, availability, processing integrity, confidentiality, and privacy.
Managed by the American Institute of CPAs (AICPA), SOC reports provide an independent, auditor-validated snapshot of your control environment, transforming your security posture from a claim into a certified fact.


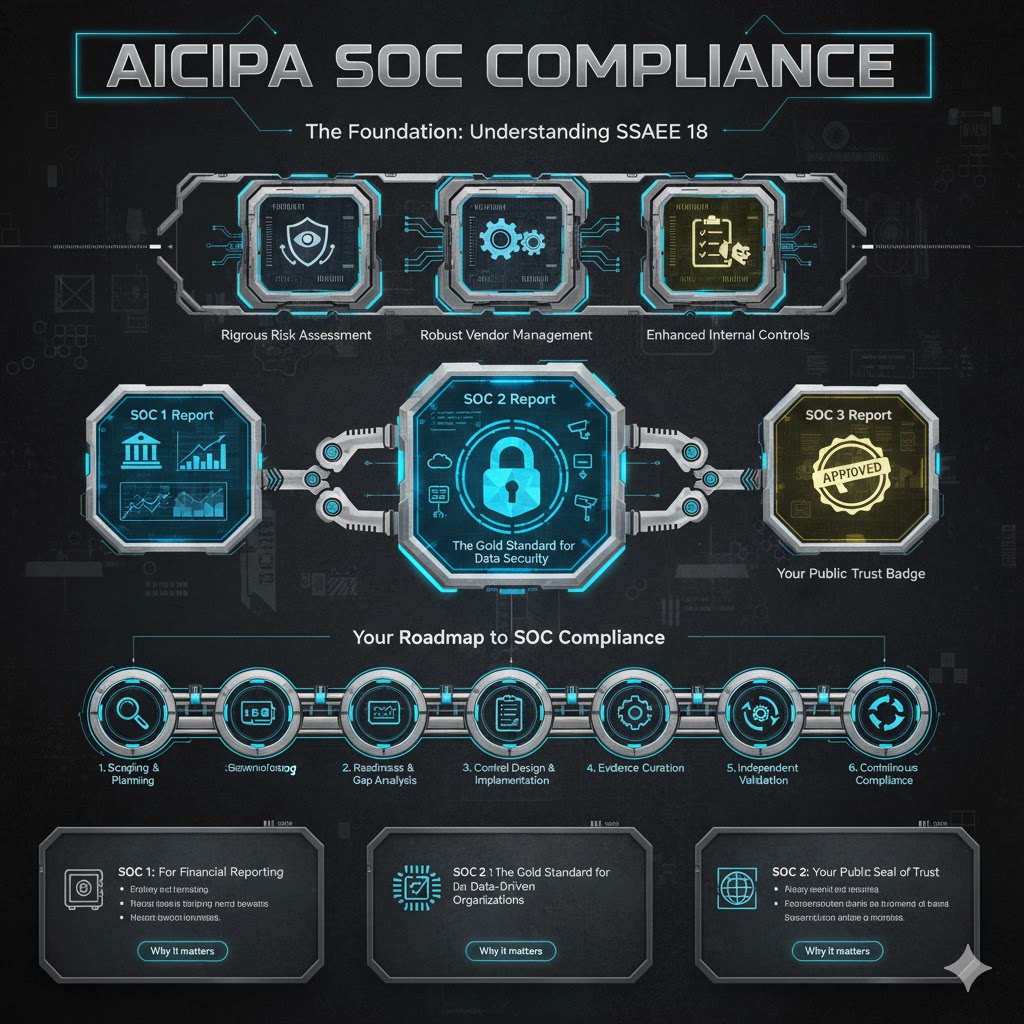
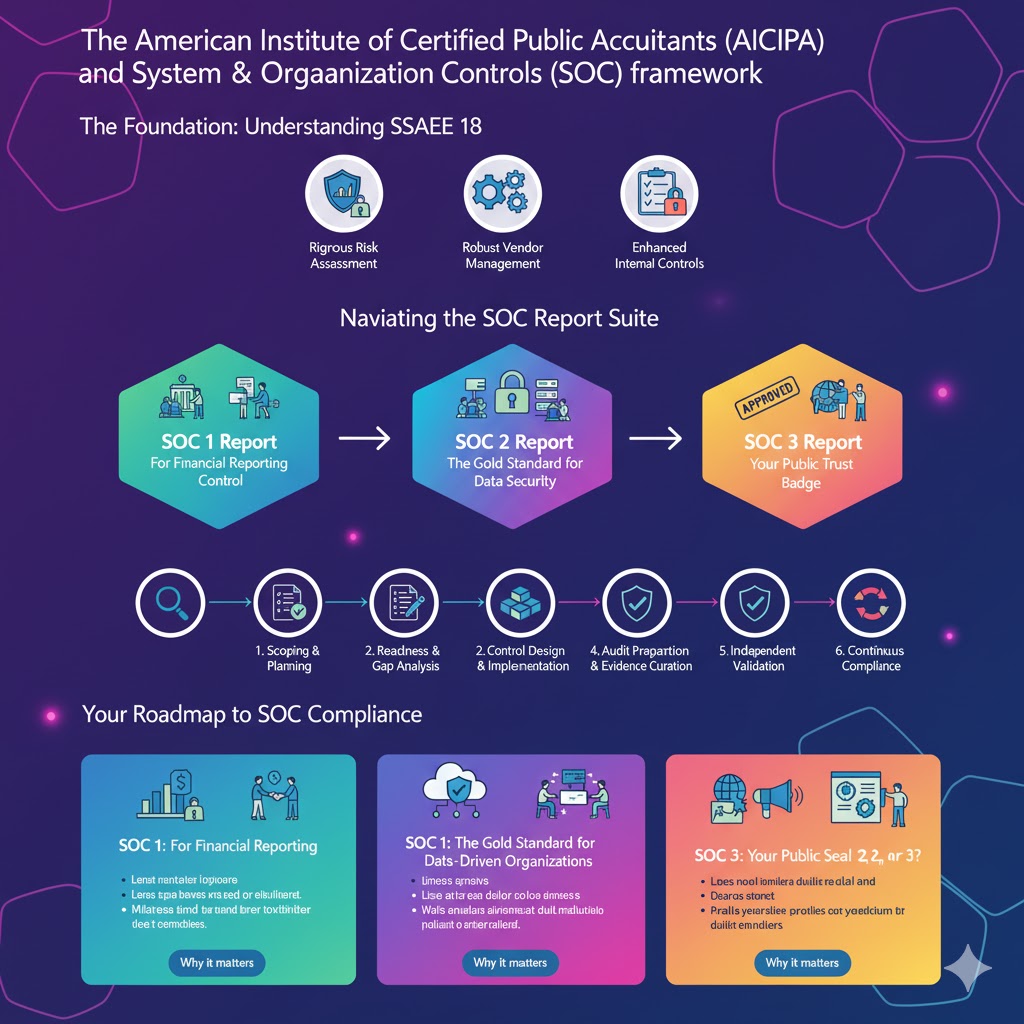
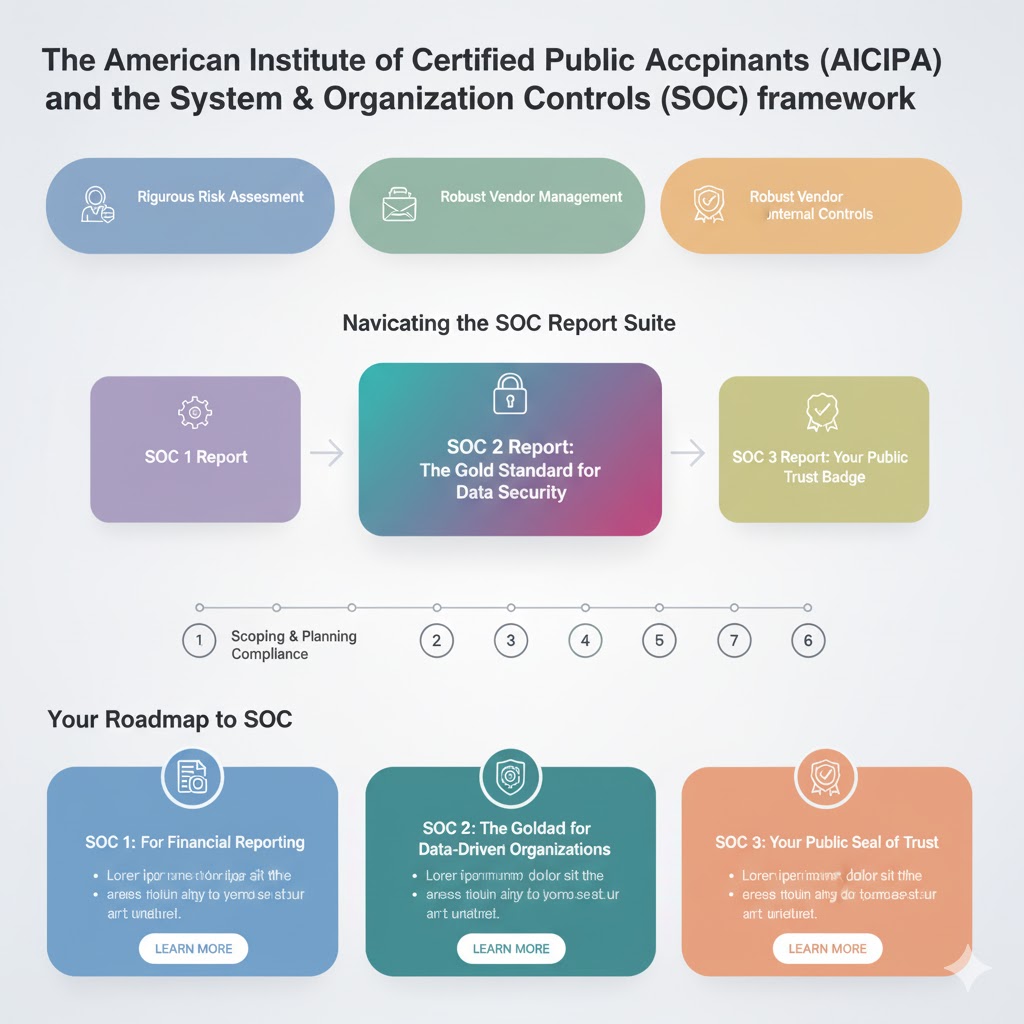
The Foundation: Understanding SSAE 18
At the heart of SOC 1, 2, and 3 reports is the SSAE 18 auditing standard. Think of SSAE 18 as the rulebook auditors follow to ensure their examinations are thorough, consistent, and reliable.
This standard elevates the quality of SOC reports by emphasizing:
- Rigorous Risk Assessment: Identifying and addressing potential threats to your systems.
- Robust Vendor Management: Ensuring your own suppliers meet high-security standards.
- Enhanced Internal Controls: Creating a structured framework for data protection.
In short, SSAE 18 is the methodology, and a SOC report is the product that gives your clients confidence.
Navigating the SOC Report Suite: Which One is Right for You?
There are three main types of SOC reports, each designed for a different audience and purpose.
SOC 1 Report: For Financial Reporting Control
- Focus: Exclusively on controls relevant to a user’s financial statements.
- Ideal For: Service organizations that impact their clients’ financial reporting, such as payroll processors, claims administrators, or payment gateways.
- Key Benefit: Provides assurance to your clients and their auditors that their financial data is processed accurately and securely.
SOC 2 Report: The Gold Standard for Data Security
- Focus: On operational controls related to security, availability, processing integrity, confidentiality, and/or privacy—collectively known as the Trust Services Criteria.
- Ideal For: Technology companies, SaaS providers, cloud hosting firms, and any organization that stores or processes client data.
- Key Benefit: A detailed, restricted-use report that gives your enterprise clients deep insight into your security practices, making it a critical tool for building B2B trust and winning large contracts.


SOC 3 Report: Your Public Trust Badge
- Focus: On the same Trust Services Criteria as SOC 2, but presented as a high-level, general-use report.
- Ideal For: Public marketing and broad distribution. It’s a seal of approval you can display on your website to assure all stakeholders of your security commitment without revealing sensitive operational details.
- Key Benefit: A versatile tool for building brand trust with a wider audience, including potential customers and partners.
Why Pursue SOC Compliance? It’s a Strategic Business Move
Achieving SOC compliance isn’t just about passing an audit; it’s about future-proofing your business.
- Win More Business: A SOC 2 or SOC 3 report is often a non-negotiable requirement in enterprise RFPs and vendor security questionnaires.
- Simplify Sales Cycles: Accelerate due diligence by providing an independent, trusted report instead of completing countless security assessments.
- Strengthen Security: The process itself helps you identify and fix gaps, creating a more resilient and secure operational environment.
- Build a Trusted Brand: In a world of data breaches, a SOC report is tangible proof that you are a secure and reliable partner.

How We Guide Your Journey to SOC Compliance
We simplify the path to certification. Our services are designed to turn a complex process into a streamlined, strategic project.
- Gap Analysis & Readiness Assessment: We evaluate your current controls against the relevant SOC criteria to identify exactly what needs to be done.
- Control Implementation & Remediation Support: We help you build and refine the policies, processes, and technical controls required for compliance.
- Audit Preparation & Partnership: We prepare you for a smooth audit, working alongside you and your auditor to ensure a successful outcome.
Your Roadmap to SOC Compliance: A Clear, Collaborative Journey
Earning a SOC report is more than just passing an audit—it’s a transformative process that builds a foundation of trust and security. We’ve designed a clear, step-by-step pathway to guide your organization from initial exploration to successful certification and beyond.
Here’s how we partner with you to achieve and maintain SOC compliance:

Phase 1: Strategic Scoping & Planning
We begin by understanding your unique business landscape. Together, we’ll determine the most valuable type of SOC report for your goals—whether it’s SOC 1 for financial controls, the detailed SOC 2 for operational security, or the public-facing SOC 3. This ensures your efforts are focused and aligned with what your clients and market expect.
Phase 2: Readiness & Gap Analysis
Before the official audit, our experts conduct a thorough diagnostic of your current control environment. We identify gaps against the relevant SOC criteria and provide you with a clear, actionable roadmap to compliance, saving you time and resources down the line.
Phase 3: Control Design & Implementation
This is where we roll up our sleeves and build. We collaborate with your team to design and implement robust, sustainable controls across critical areas like data encryption, access management, and incident response, turning policy into practice.
Phase 4: Audit Preparation & Evidence Curation
We help you tell your compliance story with clarity and confidence. Our team assists in compiling all necessary documentation and evidence, ensuring you are fully prepared for a smooth and efficient audit process.
Phase 5: Independent Validation
We stand by your side as an independent, AICPA-certified auditor conducts the formal examination. This crucial step validates your security posture and results in the authoritative SOC report that certifies your commitment.
Phase 6: Continuous Compliance & Improvement
Our partnership doesn’t end with a report. We provide ongoing support to help you monitor controls, adapt to changes, and maintain compliance year-round, making future audits simpler and reinforcing perpetual trust.

Why Our Process Works
We don’t believe in a one-size-fits-all checklist. Our methodology is built on partnership, expertise, and a shared goal: to embed security into your culture and make compliance a competitive advantage.
Ready to build trust that wins business? Let’s chart your path to SOC compliance together.
Finding Your Fit: SOC 1, SOC 2, or SOC 3?
SOC 1: For Organizations at the Heart of Financial Reporting
Ideal for: Companies that directly impact their clients’ financial statements.
You might need SOC 1 if you’re a:
- Payroll processing provider
- Claims administration company
- Payment processing firm
- Financial technology (FinTech) platform
- Third-party accounting services provider
Why it matters: SOC 1 provides crucial assurance to your clients and their auditors that your internal controls over financial reporting are robust and reliable. It’s the foundation for trust in financial partnerships.
SOC 2: The Gold Standard for Data-Driven Organizations
Ideal for: Technology companies and service providers that handle customer data.
You might need SOC 2 if you’re a:
- SaaS (Software-as-a-Service) company
- Cloud hosting provider
- Data center operator
- Managed IT services provider
- Any organization storing sensitive client information
Why it matters: SOC 2 validates your adherence to the rigorous Trust Services Criteria—security, availability, processing integrity, confidentiality, and privacy. It’s the detailed proof enterprise clients require during vendor due diligence.

SOC 3: Your Public Seal of Trust
Ideal for: Organizations wanting to publicly demonstrate their security commitment.
You might need SOC 3 if you:
- Want to display security credentials on your website
- Serve a broad customer base that values security assurance
- Need a marketing-friendly trust badge
- Want to complement your SOC 2 with a public-facing version
Why it matters: SOC 3 provides the same independent validation as SOC 2 but in a simplified, publicly distributable format. It’s your security seal of approval that builds confidence across your entire stakeholder ecosystem.
Why Partner With Us for Your SOC Compliance Journey?
Choosing the right SOC framework is just the beginning. As your dedicated compliance partner, we bring:
Strategic Guidance
Our experts don’t just understand SOC standards—we understand how they apply to your specific business model, helping you select the most valuable path forward.
Tailored Implementation
We recognize that no two organizations are alike. Our solutions are customized to fit your unique operational landscape and business objectives.
End-to-End Partnership
From initial assessment to final report and beyond, we walk alongside you, transforming complex requirements into achievable milestones.
Deep Standards Expertise
With specialized knowledge across AICPA standards including SSAE 18, we ensure your compliance isn’t just achieved—it’s built to last.
Business-First Approach
We view SOC compliance not as a checkbox exercise, but as a strategic investment that enhances your security posture, builds client confidence, and creates competitive advantage.
Ready to Build Trust That Opens Doors?
Whether you’re pursuing your first SOC report or looking to streamline your ongoing compliance, we’re here to help you build the foundation of trust that today’s business environment demands.
Let’s discuss which SOC framework aligns with your business goals and start building your compliance strategy today

